LOLBIN Decoder – Analyst-Focused Windows Command Analysis Platform
🧠 Overview
LOLBIN Decoder is a full-stack web application developed entirely from scratch during my college internship at the Instituto Superior de Engenharia de Coimbra (ISEC).
The project was designed to assist security analysts in understanding and validating Windows command-line executions, with a particular focus on Living Off The Land Binaries (LOLBins) — legitimate system binaries frequently abused by attackers to blend malicious activity with normal system behavior.
Despite the limited timeframe of the internship, the application was implemented end-to-end, including backend logic, database modeling, authentication, deployment, and security testing.
A detailed technical report describing the architecture, design decisions, and implementation is included in the repository.
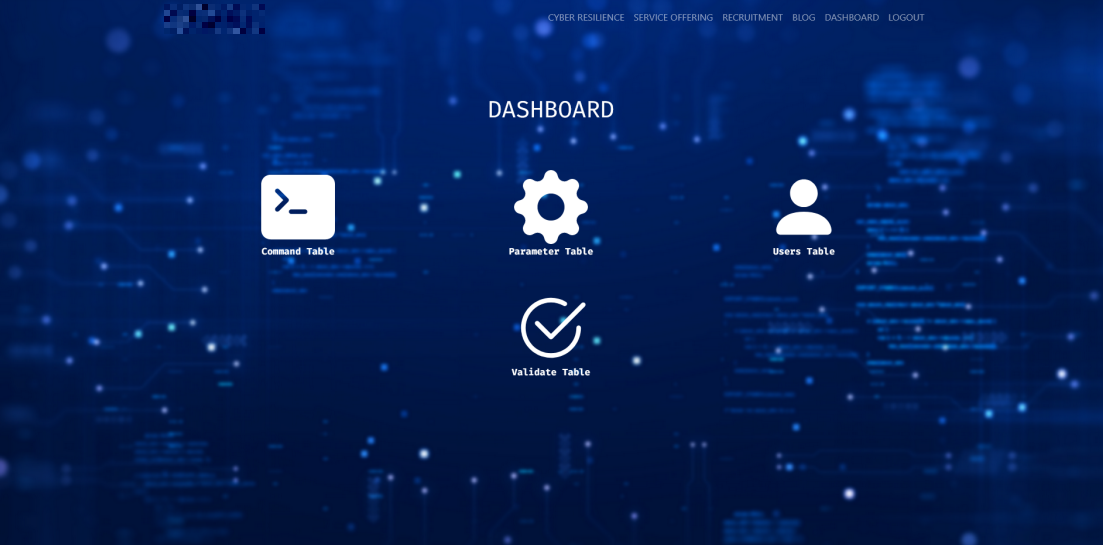
📸 Application Dashboard
An anonymized dashboard view of the LOLBIN Decoder platform, showcasing analyst-oriented functionality such as command management, parameter configuration, user administration, and validation workflows.
Note: All screenshots have been anonymized to remove organizational branding and sensitive information.
🎯 Project Objective
Security analysts often encounter Windows commands that appear legitimate but may be abused for malicious purposes. Accurately determining intent typically requires understanding:
- The binary being executed
- The parameters used
- Known abuse techniques and attack patterns
The objective of this project was to create a centralized platform capable of dissecting Windows command lines, correlating their components with structured database information, and presenting contextual security insights to support defensive analysis.
🔍 Key Capabilities
- Submission and analysis of Windows command-line executions
- Identification of LOLBins (Living Off The Land Binaries and Scripts)
- Contextual explanation of command behavior and abuse potential
- Database-backed modeling of commands, parameters, and validations
- Analyst-oriented dashboard for managing commands and metadata
- User authentication and session management
🏗 Architecture & Design
The application follows a modular and maintainable Flask architecture, including:
- Application factory pattern
- Blueprint-based routing
- SQLAlchemy ORM for database abstraction
- Flask-Login for authentication and session handling
- Flask-WTF for secure form handling and validation
- Secure password hashing using Werkzeug
This architecture enables scalability and allows the platform to evolve as new commands, parameters, and validation logic are introduced.
🛠 Technology Stack
- Backend: Python, Flask
- Frontend: HTML, JavaScript, CSS (Jinja2 templates)
- Database: SQLAlchemy (SQLite/MySQL compatible)
- Security: Authentication, authorization, password hashing
- AI Integration: ChatGPT used to dynamically enrich and update command-related data
🔐 Security & Infrastructure
In addition to application development, a secure server environment was configured to host the platform. Security measures included:
- Firewall configuration
- HTTPS for encrypted communication
- Server hardening to reduce attack surface
Vulnerability testing was performed on both the web application and the server infrastructure to identify and mitigate potential security weaknesses.
📂 Source Code & Documentation
👉 LOLBIN_Decoder – GitHub Repository
The repository includes the complete source code along with a comprehensive technical report detailing the system architecture, implementation choices, and security considerations.
🚀 Future Improvements
- Integration with external threat intelligence feeds
- Automated command classification
- API support for SIEM / SOAR integration
- Enhanced role-based access control
- Improved UI/UX and reporting features
🧠 What This Project Demonstrates
- Full-stack web application development
- Secure authentication and session management
- Database modeling and backend architecture
- Practical cybersecurity knowledge applied to real-world scenarios
- Secure deployment and vulnerability testing
- Independent problem-solving under time constraints
🧪 Demo Credentials (Evaluation Only)
⚠️ These credentials are provided strictly for demonstration and evaluation purposes.
- Email:
admin@gmail[.]com - Password:
admin123